Table of Content
- Embedded Linux Security Overview
- Malware Attacks and Buffer Overflows
- Man-in-the-Middle (MitM) Attacks and Session Hijacking
- Outdated Firmware
- Conclusion
Embedded Linux Security Overview
Most people are familiar with the Linux operating system, but Linux is also distributed in a stripped-down version called embedded Linux. It’s a lightweight version of the operating system that powers many of today’s IoT (Internet of Things) devices, smart home automation products, and networking equipment such as routers and Wi-Fi hotspots. Embedded Linux uses fewer CPU and memory resources, and many of the biggest vendors have a lightweight open-source version available to the public.
Because embedded Linux is a lesser-known version of the operating system, it’s often poorly protected from hackers. This leaves the operating system vulnerable to hackers who can compromise the operating system and add malware to it or configure devices for their own malicious use. For example, embedded Linux is the target for Mirai, a botnet malware application that infects IoT devices to make them a part of a botnet to perform a distributed denial-of-service (DDoS) against internet web services. To protect embedded Linux devices from hackers, developers and device owners must know the common vulnerabilities found in IoT and mobile devices and take necessary precautions.
Malware Attacks and Buffer Overflows
The Mirai botnet is one of the most common malware applications targeting IoT, but numerous other malicious applications are available to attackers. When IoT devices are shipped to consumers, manufacturers program a default username and password so that the customer can authenticate into the device and configure it. Users often leave this default password configured, and it leaves the device open to hackers.
Hackers write scripts that scan the internet for open devices with default username and password credentials. When a device is found, hackers can authenticate into it and install malware or configure the device with their own settings. With access to the device, the hacker can then eavesdrop on data, reroute users to malicious websites, steal video and images from compromised cameras, and install malware that will send traffic to a target on command (e.g., a DDoS).
Covert access isn’t the only goal of a hacker. A buffer overflow will crash the application service on the device and execute malicious code. This malicious code could elevate privileges to administrator, run malware on the device, or steal credentials. With elevated privileges, an attacker has complete control of the device and potentially other network components. With malware injected onto the device, an attacker can perform any activity allowable by the operating system, which could be eavesdropping or turning the device into their own attack machine in a botnet.
To remedy the issue of malware and a compromised operating system, users should always change the default password on the device. When the device is reset to manufacturer settings, the password should be changed again. Never leave the default password configured on any IoT or mobile device, especially if it’s connected to the public internet.
Man-in-the-Middle (MitM) Attacks and Session Hijacking
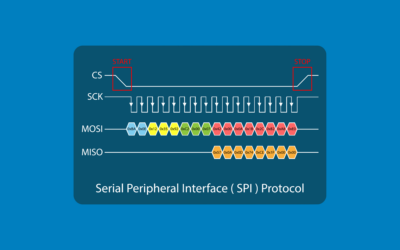
With routers that run embedded Linux, all user traffic runs through the device and gets sent to the intended recipient. An attacker with access to a router could perform a MitM attack or steal session tokens. Both pose a significant risk to users and their data privacy.
A MitM attack is often done on public internet where the hacker can perform an attack called ARP (Address Resolution Protocol) poisoning. ARP poisoning tells devices on the network that their default gateway is the attacker’s device (usually a laptop). User devices then route traffic through the attacker’s machine, and this gives attackers access to any data transmitted to the internet. If the data isn’t encrypted, it’s fully available to the attacker who can save it for future attacks such as identity theft.
To communicate with applications, servers create a session token and share it with a user’s device. This session token is used by the application to identify the user after authentication. Session tokens are also vulnerable to theft in a MitM attack. An attacker with session tokens can masquerade as the user on an application. With the session token, the attacker can perform any action in the context of the user account. The attacker can steal data, change account settings, and reset the user’s password.
Users should always connect to online applications using encryption. Popular browsers such as Chrome and FireFox warn users when they connect to a website without SSL/TLS encryption. Any time you’re on public Wi-Fi, never authenticate into sites that contain sensitive information such as banking and healthcare websites.
Outdated Firmware
The biggest risk to organizations is leaving embedded Linux unpatched. Linux vendors release patches that remediate vulnerabilities found in the operating system. Allowing these systems to remain unpatched leaves them open to the latest exploits. In most scenarios, business owners and individual users do not look at the latest vulnerability notices to identify if their devices need to be patched.
Some manufacturers set up the device for automatic updates, but this can disrupt network communication and isn’t turned on by default. Users and business owners should review equipment once a week for updates. If any firmware updates are available for your version of Linux, it should be installed as soon as possible. The longer the device goes unpatched, the larger the window of opportunity for an attacker to exploit the system. For any device available on the public internet, the window of opportunity should be as small as possible, which means patches should be installed immediately when they are released by the manufacturer or operating system developer.
Conclusion
Many users and business owners are unaware of the cybersecurity concerns with embedded Linux. If you have a mobile phone, IoT device, smart home equipment, or router in your home, then you probably have embedded Linux. Monitor the device manufacturer for updates to its firmware and install updates when they are released.
No cybersecurity standard protects you completely from risk, but you can greatly reduce the chance of becoming a victim to an embedded Linux compromise by changing the default password, using only encrypted communication on public Wi-Fi, and updating firmware when a patch is released.










0 Comments