Tech thoughts on things we love. 
Discover ideas, insights, and inspirations that drive us to explore the topics we love and the stories that shape us.
- All
- Agile
- AI
- Android
- Cloud
- Cross-Platform
- DevOps
- Digital Strategy
- Digital Transformation
- iOS
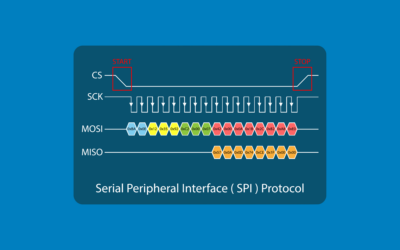
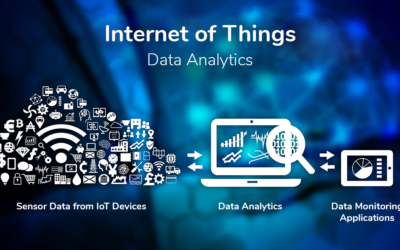
- IoT
- Mobile
- Nearshore
- UIUX Design
- Agile Testing