Table of Content
In the vast world of software development, there’s a rising demand for secure and efficient identity management. One name that stands out in this domain is “Keycloak .”But what exactly is Keycloak, and why is it gaining such traction among developers?
Keycloak is a robust Identity and Access Management (IAM) solution that offers multiple features to authenticate, authorize, and manage users. It seamlessly integrates with modern application architectures, providing an efficient and flexible way to manage users’ identities and access. Its capacity is evident, especially when you aim to develop applications that need reliable authentication and authorization mechanisms but want to avoid the intricacies of complex coding.
What is Identity and Access Management (IAM)?
Identity and access management (IAM) encompasses a framework of policies and technologies designed to ensure that the right individuals within an organization have the appropriate access to technological resources.
Keycloak Features
- Single Sign-On (SSO): Keycloak supports Single Sign-On, meaning users only have to log in once to access various applications.
- Identity Brokering: This allows Keycloak to connect to other identity providers to use their authentication.
- Social Login: Users can log in using their social media accounts.
- User Federation: Connect to multiple user databases and sync users or authenticate against them.
- Fine-Grained Authorization: Keycloak can be used to add fine-grained permissions to applications and services.
- Adapters: Keycloak provides client adapters for different programming languages and platforms.
- Admin Console: A user-friendly interface for managing realms, roles, permissions, and more.
Keycloak Core Components
- Realms: Realms are a way to manage isolated sets of users, sessions, and clients.
- Organizational Flexibility: Realms allow you to segment users, sessions, and clients based on departments, teams, projects, or organizational structure, making it easier to manage authentication and authorization separately for different groups.
- Multi-Tenancy: By treating each realm as a tenant or a namespace, Keycloak becomes a solution suitable for multi-tenant applications where you want to keep user data and configurations distinct for each tenant.
- Customization: Since each realm can have its own set of users, roles, and clients, you can tailor the authentication experience (like login themes, password policies, etc.) to specific realms.
- Clients: In Keycloak, a client is an entity that can request user authentication. It could be a web, mobile, or any other application.
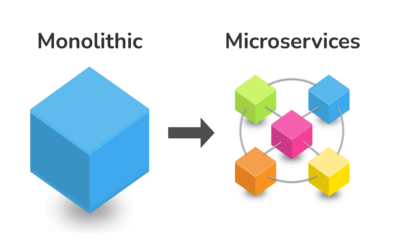
- Versatility: The broad definition of a client in Keycloak means it can accommodate various application types – web apps, mobile apps, microservices, and more. This offers a one-size-fits-all approach to authentication.
- Centralized Management: By treating every application as a client, Keycloak centralizes the management of all authentication requests, reducing redundancy and enhancing security.
- Roles: Roles are a way to group permissions. Users can be assigned roles, which determine what actions a user can perform or what resources they can access.
- Granular Access Control: Grouping permissions under roles allows for fine-grained control over what users can and cannot do. It simplifies the process of access management.
- Consistency: Using roles allows you to maintain consistent access patterns across various applications and realms. For instance, an “admin” role in one application can be designed to offer similar privileges in another.
- Dynamic Assignment: Roles can be assigned to users dynamically based on various factors like user attributes, group membership, or even external identity providers, making the access management adaptive.
- Users: These are the end-users who authenticate and interact with the clients.
- End-User Centricity: By focusing on the end-user, Keycloak ensures that authentication and access experiences are seamless for the user, improving user satisfaction.
- Profile Management: The Users component offers a centralized place for managing user profiles, credentials, and attributes, streamlining the management process.
- Extensibility: The user component in Keycloak can be integrated with other external user databases or identity providers, ensuring flexibility in user management.
How Does Keycloak Work?
Keycloak operates on the principles of OpenID Connect and OAuth 2.0 protocols, enabling a standardized approach to identity and access management (IAM). Here’s a step-by-step breakdown of how the process evolves:
- Access Request: A user tries to access a protected resource, such as a web app or an API endpoint. Since the user hasn’t been authenticated, the application recognizes this and redirects the user to the Keycloak authentication server.
- Keycloak Login Page: The user lands on the Keycloak login page (or a custom login page you’ve defined in Keycloak). If multi-factor authentication or social logins are configured, users might also see options or prompts for those.
- Authentication: The user provides their credentials (like username and password) or uses an alternative authentication method (like a social login). Keycloak validates these credentials against stored user data or any external identity provider configured (like LDAP or Active Directory).
- Token Generation: Keycloak issues a token, typically a JWT (JSON Web Token), upon successful authentication. This token is a compact, URL-safe representation that transfers claims between two parties. It contains encoded information about the user, the issuer, and any specific permissions or roles granted to the user.
- Token Return: This token is then sent back to the user’s browser, usually as a part of a redirect to the original application or resource they tried to access.
- Resource Access: Armed with this token, the user presents it to the application or resource they wish to access. The application decodes and verifies the token (ensuring it’s valid, hasn’t expired, and was issued by a trusted source, i.e., Keycloak).
- Authorization: Beyond just authentication, the token can also contain roles and permissions specific to the user. The application checks these roles/permissions to decide what the user can and cannot do within the application.
- Session Management: Keycloak manages user sessions, ensuring the user doesn’t have to log in for different applications within the same realm repeatedly. If the user logs out or an admin revokes their session, they must authenticate again.
- Token Refresh: Depending on the token’s lifespan, it might expire after a certain time. Keycloak can be set up to provide refresh tokens, allowing users to get a new access token without going through the full authentication process.
Why Use Keycloak?
- Versatility: Keycloak can be used with almost any modern application and service.
- Standards-Based: It supports standard protocols like OpenID Connect, OAuth 2.0, and SAML 2.0.
- Customizable: Keycloak can be extended and customized as needed.
- Open Source: This makes it a cost-effective choice for organizations and ensures broad community support.
Deployment and Integration
Keycloak offers versatile deployment options, including as a standalone server, within a Docker container, or on Kubernetes. Before 2022, client applications relied on Keycloak client adapters for integration. These adapters are now deprecated. As alternatives, developers have turned to NPM modules or Spring Security (for those utilizing Spring Boot) based on the specific environment of their applications.
- NPM Modules: Best suited for Node.js applications written in JavaScript/TypeScript. If you’re developing a Node.js application, using an NPM module might be more straightforward and keep you within the JS ecosystem.
- Spring Security: Ideal for Java-based applications, especially those using the Spring framework. It offers a comprehensive, enterprise-grade security framework that integrates smoothly with Keycloak using the provided adapters. Learn more about using Keycloak using Spring Boot.
NPM (Node Package Manager) modules or packages are libraries or sets of reusable code that can be used in Node.js environments. These modules can serve various purposes, from utility functions to integration with services like Keycloak.
Harnessing Keycloak’s full potential requires understanding its capabilities and leveraging existing NPM modules for Keycloak integration.
Learn more about Krasamo’s Open Source NPM Module for Keycloak Integration and how our NPM module can bridge your application with Keycloak’s capabilities for a smooth and secure user management experience.
Keycloak Container
Keycloak can be containerized for deployment, scaling, and management. When discussing “containers,” we refer to Docker and orchestration platforms like Kubernetes.
You can run Keycloak in a container using the Docker official image on Docker Hub. This image encapsulates the Keycloak server, database, and its required environment and dependencies.
Keycloak supports several integration points with container orchestration platforms, such as Kubernetes. This makes it easy to manage Keycloak in a Kubernetes cluster.
Running Keycloak in containers has many portability, scalability, reproducibility, and security benefits. Learn more on how to run Keycloak in containers.
Keycloak Typescript Libraries for Node.JS Projects
Various tools and platforms have emerged to fortify and streamline user management processes in the evolving digital authentication and security landscape. As developers continually seek to refine their toolkits, Krasamo has launched its open-source library – the Keycloak-Typescript. Specifically tailored for Node.js projects, this library highlights the strengths of Keycloak, making integrations more efficient and developer friendly. As we search deeper into this product, we’ll explore its unique features, its simplifying capabilities for Node.js developers, and its commitment to open-source principles.
Want to learn more about integrating Keycloak with your applications? Need Keycloak consulting services? Contact us for more information.












I’m low-key obsessed w/ this post on Keycloak-Typescript! 🤩 Krasamo’s efforts in making it dev-friendly is totally on point! 👏
I must commend the author for covering the subject matter thoroughly, especially concerning containerization with Docker and Keycloak. However, a mention of Identity and Access Management (IAM) would have been beneficial, as it’s an integral aspect of leveraging Keycloak’s full potential.
I thoroughly enjoyed this informative blog post! The explanation of Keycloak’s token refresh feature and its versatility in supporting standard protocols like OpenID Connect and OAuth 2.0 was particularly insightful.
I appreciate your introduction to Keycloak, which I’ve utilized in previous projects as part of our company’s AWS consultancy services. However, I do feel that more context on its scalability would be beneficial for a broader audience.
I completely agree that providing more context on Keycloak’s scalability would be beneficial for readers. Given the feature of realms, which allow for the segmentation of users and clients based on organizational structure, I believe it’s reasonable to assume that Keycloak can scale to accommodate large enterprises. In a cloud consulting services context, this flexibility is particularly valuable for companies with complex infrastructures. I’d love to see further discussion on this topic in future articles!
I completely agree with the notion that Keycloak is gaining traction among developers. From my experience as an AI engineer, I can attest that its robust Identity and Access Management (IAM) capabilities make it an attractive solution for modern application architectures. In fact, cloud consulting services are increasingly recommending Keycloak due to its seamless integration and flexibility in managing user identities and access. The ability to avoid complex coding while ensuring reliable authentication and authorization mechanisms is definitely a plus. Thanks for highlighting the importance of IAM!
I’m not surprised you’d recommend leveraging NPM modules for Node.js applications, as it’s a straightforward approach. However, for those outside the JS ecosystem, such as Java-based applications using Spring, I’d suggest exploring AWS consultancy services to optimize Keycloak integration. Specifically, utilizing Keycloak adapters with Spring Boot can provide a seamless experience. It’s worth noting that Krasamo’s Open Source NPM Module is just one of many solutions available, and a thorough evaluation of the options should be conducted before making a decision.
Just wanted to add a bit more context here. As someone who’s worked with identity management systems, I can attest that Keycloak is indeed a robust solution for authenticating and authorizing users. However, it’s worth noting that IAM isn’t just limited to authentication – it also encompasses access control, auditing, and even compliance regulations. So, while Keycloak excels at user management, it’s just one piece of the larger IAM puzzle.
I found the explanation of how Keycloak works to be clear and concise, but I would have liked to see more discussion on its integration with AWS services in an aws consultancy context. Nonetheless, a well-written post.
The integration with AWS services in an aws consultancy context could be explored further, perhaps discussing how Keycloak can complement cloud-based IAM solutions like Cognito or IAM. Would be valuable for cloud consulting services looking to implement scalable identity management.
I completely agree with the points you’ve made about Keycloak’s role-based access control. In addition to simplifying access management and promoting consistency, it also enables organizations to implement a robust security posture. I’d like to mention that an AWS consultancy can help companies integrate Keycloak with AWS services for enhanced scalability and security. This combination is truly powerful!
Great post! I completely agree that Keycloak is a powerful Identity and Access Management solution. In addition to the features mentioned, partnering with an AWS consultancy can help organizations maximize their investment in Keycloak by optimizing its integration with other AWS services like Cognito and IAM. This can further enhance scalability and security for large-scale applications.
I completely agree that the emergence of libraries like Keycloak-Typescript is a game-changer in simplifying user management processes. As a seasoned Cloud engineer, I’ve witnessed firsthand the benefits of leveraging cloud advisory services to optimize authentication and authorization flows. This library’s efficiency and developer-friendly approach aligns perfectly with modern microservices architecture. Great job, Krasamo!
I completely agree with your explanation of how Keycloak works! It’s indeed impressive how it seamlessly integrates OpenID Connect and OAuth 2.0 protocols for IAM. Have you considered leveraging AWS consultancy services to optimize your infrastructure for scalability and high availability? This would be a fantastic opportunity to further streamline the authentication process.
Love this explanation of Keycloak! It’s so refreshing to see a clear breakdown of token generation, return, and resource access. I’d like to add that cloud consulting services can also leverage Keycloak for identity and access management, making it easier to manage user permissions across multiple applications. Great job on sharing your knowledge!
I’m so stoked you shared this blog post! 🤩 I’ve been working with Keycloak on a recent project and can attest to its awesomeness 😎. Have you explored using it in conjunction with AWS Lambda functions? I’ve found that cloud consulting services, like Amazon’s own Keycloak support, can be super beneficial for large-scale implementations. Can’t wait to dive deeper into this topic! 💻
I’m so down with this blog post! It’s on point about Keycloak’s token generation and verification process. I’d like to add that AWS consultancy often recommends using a combination of Keycloak and other tools like AWS Cognito for identity management and access control in cloud-based applications. This way, devs can leverage the strengths of both services for enhanced security and scalability. Great job on breaking it down!
Hey there, I gotta respectfully disagree with the assertion that NPM modules are the only way to integrate Node.js apps with Keycloak. Haven’t we seen some impressive cloud consulting services leveraging custom-built solutions? Wouldn’t it be beneficial to explore those options as well? Can you share more about why NPM modules are the preferred choice here? 🤔